-
Posts
21,649 -
Joined
-
Last visited
-
Days Won
119
Content Type
Profiles
Forums
Events
Everything posted by Rodney
-
Webster is a busy guy!
-
This may be of interest to those who need more realistic characters... of a variety of body types. It was previously reported that Adobe had acquired Maximo and the latest news shows plans moving ahead to provide Fuse software with Adobe CC. Fuse is a bipedal set of tools used with Maximo (and other software) used to create characters. It's similar in many ways to MakeHuman and other software. For geometry the characters can be exported as OBJ. For animation the preferred format is FBX. In something that reminds me much of Hash Inc's earlier ground work with segmented models, the highlights of Fuse are the quick modification of modular characters (those provided or those you supply via import) to create characters of almost any type (bipedal being the focus). Fuse also leverages Substance's API to apply procedural textures to clothing which is easily customizable as well. How can these characters best be used with A:M remains to be seen but there are some very interesting approaches being used. Fuse (preview) comes with Adobe CC subscription and as far as I can tell will remain part of Adobe CC offer. Joe McPeak of Truebones has a video where he explores Fuse's workflow (I'll see if I can find a link). Here's another from Adobe: http://www.adobe.com/creativecloud/features.html?trackingid=226KD1P6&mv=email#fuse-cc-whats-new Of particular interest is Fuses use of UV layout to control customization of characters and layering of images/maps to drive the topology of meshes to include removal of unnecessary geometry under clothing. In A:M the latter might is fairly equivalent to setting geometry underneath clothing to transparent and hiding it so that extraneous calculations need not be performed.
-
Agreed. Over the years I've noticed a lot of software with similar approaches to drilling down to more complex information but few (none?) as refined and intuitive as that of A:M. I do reserve some serious affection for the technology (and vision) underneath the hood that makes the PWS in A:M integrate so well across the board. As Martin once said, he built everything with animation first and foremost in mind... all other things of necessity follow. This has been a perennial problem in software where animation is a byproduct. In recent years most software is being written from the ground up with a more animation-centric view in mind. But this will always translate to workflow relative to the underlying technology. Are you familar with the story of Moses and Aaron who went before Pharoah? Aaron cast down his rod which became a snake and the magicians of the court did likewise with their enchantments. In the end only one snake was left; having consumed the others. Someone had superior technology (thought craft).
-
A:M isn't trying to catch up... it's waiting for the world to catch up. With proper technology in place spline/patch technology can then enter into the next phase of advancement. I liken this to Ed Catmull's telling of how they charted the course to create the first digitally animated feature film and laid out their plan to get there. He/They saw that with advancements in computing following Moore's Law it would be a specific amount of time before they would be able to succeed in their endeavor but that it would (without any doubt) inevitably happen... if they were there to see it occur. So his effort then focused more fully on survival... of keeping his team together during the long haul it would take to get from where they were then into the future. Of course this does't mean they were idle... they set out to more accurately define what their place would be in that future. Why is it that folks like A:M's workflow so much? (often wishing they had A:M's workflows and ease of use in their daily work-a-day solutions) Could it have anything to do with the technology (and the vision) behind the tools? It's not surprising that folks use other software. What is a bit disappointing is that when folks (inevitably?) do they stop supporting A:M. Would I be any different? If I were happily churning out animation at PIXAR, Dreamworks, or any number of animation studios would I still financially support development of A:M? While reality often suggests otherwise, I'd like to think that I would. Note: I make a distinction between general/moral support (that of what is demonstrated by Webster Colcord) and financial support (of which there is no indication that he ever contributed) although I'm sure all support is appreciated. General support is a great thing but its good to remember that it takes money to support the people behind the effort to develop software at the pace we would prefer. Lacking that support what other options are available.
-
It's nice to see some of the many folks who cut their teeth with Animation:Master give credit where due to the creators of A:M. 'Antz' was one of the first CG films that proved that =other companies- besides Pixar could rise to the challenge of digital animation. It was certainly one of the first that convinced me that high quality animation wasn't out of the reach of mere mortals. And it should be no surprise that the artists behind these earlier films helped drive better software and workflow through their desire to have a better solution... one more like the approach they had in Animation:Master. There are some recent demos from Pixar that show some newer capabilities that suggest in many ways they are only now catching up to some of A:M's 'self evident' and intuitive workflows. In other words, in many ways A:M is still ahead of its time.
-
Nice! Even way back then you were meticulous.
-
Very nice!
-
Great stuff Matt! And thanks for sharing the resources!
-
Here's a brief but good article from the Animated Spirit Blog: http://www.animatedspirit.com/the-five-phases-of-work/ Overview: Phase One: Beginnings Phase Two: Preparation and Planning Phase Three: Doing the work Phase Four: Struggle Phase Five: Completion This process is not unlike any good story-telling worth being told. I can easily see overlap between the phases that suggests similarity between the three (and often four) act structures of theater/film production. And (because things in collections of 5s seem to be important) don't forget to read James Chiang's five part review of the book 'Five Cs of Cinematography'. It's very well worth the look. Here's part 5; Composition: http://www.animatedspirit.com/book-review-the-five-cs-of-cinematography-part-5-composition/
-
- 1
-

-
The latest trailer for Disney's 'The Good Dinosaur' has been released (Trailer 2): Xhttps://www.youtube.com/watch?t=141&v=daFnEiLEx70 At lot of shots from the previous trailer but some new ones too!
-
I'm glad to hear the waters are receding. It looks to me like a breach/partial breach of Beaver Dam was/is a major contributor? Hang in there.
-
Awesome! Nicely done.
-
Finally, I have seen your video Robert (after the sidetrack into forum permission corrections) Excellent tutorial and just what the doctor ordered for my Bone Falloff deficit!
-
I get something similar. Perhaps that is a glitch with IPB and post lengths? I do see that if I Right Click on Edit and select 'Open in new window' the post correctly opens for editing. So, try that.
-
Interesting. I can't see anything that would be private in those topics. I believe those topics (in the private area) were being prepped for final refinement and (re)publishing as a form of updated documentation. As the champions of that particular documentation project have moved on to other endeavors it's safe to say they can and should be placed back in the pool of general information. I'll collapse a few extraneously deep branches within the A:M Answers area as well.
-
Thanks Matt, That helps. It may also explain why some of the concept is sketchy to me, namely that much of the Bone Falloff (initially) is automated (by the default settings).
-
Thanks Robert. Interestingly, I don't have permissions to wherever that link goes. I'll have to look into that.
-
I am realizing that this simple concept (Bone Falloff) is eluding me in ways I can't quite express. Is there a reference or example of ideal use for Bone Falloff? Alternatively, perhaps someone can walk me through a basic usage scenario? This is opposed to CP weighting except that I assume CP weighting is actually a means to define/refine Bone Falloff. Sorry if this is too vague a question. It seems to me that Bone Falloff should be a very simple concept and yet that simplicity eludes me. As such I'm looking for a very basic use case/example that demonstrates the basics.
-
It may be worth noting that regardless of the FPS... a second is still a second. That may seem a silly thing to say but with all things considered until the content of that second is either extended or shortened it can be hard to perceive what has been added or taken away. This relates to the findings of traditional animators who on more than one occasion found animation on twos to 'play' better. That is to say the repetition of a frame rather than a replacement of that frame to suggest movement of some object or shape within that frame. As an example; one might gain a 50FPS rate by simply duplicating each frame from a 24 or 25 frame sequence. (as you've mentioned in your first post... that of 50FPS being double that of the PAL frame rate. I suppose the question to ask might be, "What is changing from frame to frame that benefits from or requires the faster frame rate"? This relates to the observation traditional animators had with panning backgrounds and character walk cycles. They found that animating on twos resulted in noticeable slippage as the background moved. If attempting to move the background at the slower pace of twos the effect was a stutter/strobe which was very noticeable. So, animators began to form a rule of sorts that where a character interacted with a background animation would be drawn on ones. If no contact was present the shots could be animated on twos. How does this approach translate to higher frame rates? I'm not entirely sure but I'd guess that many of the same general rules/theories apply. Of course it does help that by their very nature computers animate everything on ones... BUT... that doesn't mean actions/activity within the shot isn't technically still on twos... threes.. whatever. How fast is the object moving? How much is the object changing? How long does the action need to be held (or put into a moving hold) in order for the audience to 'see' what is there? In Richard William's book 'The Animator's Survival Kit' he talks about a young animator that tried to animate a character yawning. He drew all the poses correctly but the timing... that rate of presenting frames... was ZIPPPP! entirely too short and didn't get better with his attempts to fix the animation. The underlying reason was that he was trying to present the animation in too short a time frame. So, a final set of questions might be; what will be animated in those frames and given that information how long will that whole shot/sequence then be required to be? I would think that of interspersing odd frames (subliminal message types stuff) and using subtlety/similar shape/themes (illusory visuals) the latter would yield the more effective results. A classic example of a problem with subliminal messages is that they may be too subliminal; ex: the gorilla walking amongst a bunch of people playing basketball that no one in the audience perceives.
-
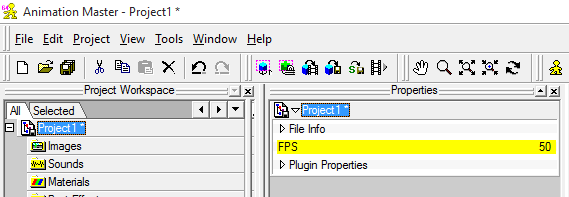
I'm not sure about playback options but we can definitely set our projects to 50FPS in A:M. Just Right Click on the Project container in the Project Workspace (at the very top) and set the FPS to the desired framerate.
-
Hey Al! Many of your questions can be answered with a 'Yes, but...' which relates to the many differences between polygon approaches and spline patch modeling and animation. As you've grasped there are a lot of things you can do via import of OBJ (and as Nemyax adds... converting from other models) but there's not much of a better way to resolve those than to dive in and see what works best. Much will depend on what you plan to place in your scenes (as static objects) and what you expect to animate (or articulate). Here's a rough attempt to answer your queries: 1) A:M has several tools that allow movement of Control Points on a surface. If the surface is in a cardinal direction this will be considerably more straightforward as keys can be held down in order to move any CP, shape or object in a given direction along a spline. Sliding CPs along a spline in any arbitrary direction... hmmmm... I think we can do that but I haven't used it in my workflow. In the past few years there have been several tools added that allow projection of CPs onto surfaces (or send them to specific locations) that may also fit the bill. As far as my workflow I'd say use of the 4 key to move a CP along a spline is likely the most common. 2) A:M has some very basic tools for this (such as the Cut Plane plugin) but the lack of density in most spline models which is usually of benefit can work against us in that regard. As such it can be hard to maintain curvature of a given spline. One approach to cutting models would be to use another program to do the cutting and then import that into A:M for placement or further refinement. 3) The Dopesheet still works for lipsync (and as has always been the case) can drive any poses. The dictionary can be amended/edited as desired. 4) I tend to work in low rez so I'm not the best to answer this one but in general you can render to as high a rez as your system/RAM will allow. I will add that Netrender... which was separate software in the $500 range when you were using A:M... is now packaged with A:M so you can launch a variety of renders in various formats and have them all render simultaneously. 5) This 'retopology' tool is know as 'Snap to Surface' and can be used to place CPs/splines onto the surface of any prop or patch model. A Prop being in this case being any imported OBJ, STL, 3DS... and a few others). 6) I don't see any issues there but will defer to others with NVidia cards. 7) Yes, I'm sure there will be but the good news is that we'll work through them together one gotcha at a time. You've been missed. It'll be great to have you back!
-
Nerdwriter has a piece on 'Nighthawks' that was just released. And of course it immediately made me think of Rodger's work here. xhttps://www.youtube.com/watch?t=5&v=7j5pUtRcNX4
-
I'd love to investigate using OBS for live streaming but confess that it's beyond me at this moment. I'm not sure if that is more for lack of interest or just because I'm lazy. I suspect that latter because I do have some interest.
-
Bottom line up front: Everyone needs some type of video capture software. There are a lot of screen capture programs and utilities out there and each one has it'd pros and cons. There are so many in fact that I've debated running something of a comparison in order to highlight some of the options. But... since such a comparison will take considerable time and a lot of information is already available via a quick google... for now I'll just point to yet another of the options. Atomi Active Presenter is a program that I don't recall highlighting and it is one of the more powerful ones out there because in addition to screen/video capture it also has some basic video editing capability that isn't seen in other free capturing software. In my estimation it fits in just below Camtasia with regard to capabilities and in some areas outperforms there also. The caveat is that to get to those additional features users have to opt for 'standard' or 'professional' editions ($199 and $299 respectively). The primary differences between free and paid versions is export capability where video presentations can be immediately exported to a variety of document formats (PDF, DOC, XLS, PPT, etc). The free version of Active Presenter is more than useful and for those without video capture capability it will be well worth looking into. If you are looking for a good video capture software definitely check it out: http://atomisystems.com/ http://atomisystems.com/activepresenter/features-comparison/ Of course with any software that has tiered releases (i.e. hobble-ware) it can be frustrating to look at grayed icons for features that aren't activated in your particular tier. Active Presenter is very useful without these additional features but if such things frustrate or aggravate it may be best to move on to other options. Other options? Here's one I haven't covered before: https://getsharex.com/